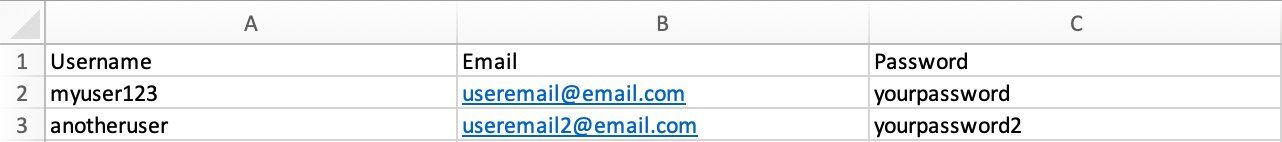
When you sign up on most websites, your data will be stored in a database table. This table will typically include your username, email, password and any other details the website has on you.
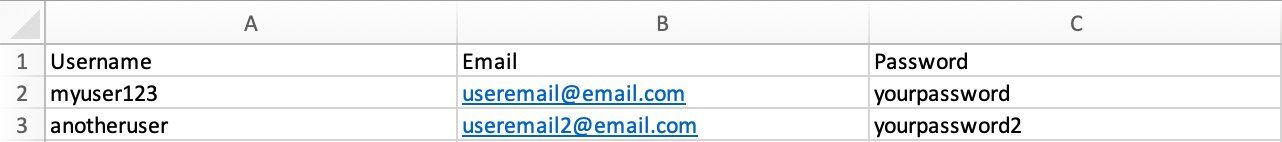 Each time you return to the website and try to log in, the user table will be cross-checked against what you have inputted to find a match. Thousands of users can be stored in a single table so they are a key target for hackers looking to exploit the data and sell on via a black-market.
Passwords
The safest presumption we can make is that your password will be passed to a hacker at some point or someone with malicious intent. Commonly, a third-party website you use will be exploited and reveal your email and password in a leak. Many high-profile cases of data leaks have been highlighted over the years in the media.
You can check if your email has previously been included in a data breach via the website found here.
Best practices for passwords:
Each time you return to the website and try to log in, the user table will be cross-checked against what you have inputted to find a match. Thousands of users can be stored in a single table so they are a key target for hackers looking to exploit the data and sell on via a black-market.
Passwords
The safest presumption we can make is that your password will be passed to a hacker at some point or someone with malicious intent. Commonly, a third-party website you use will be exploited and reveal your email and password in a leak. Many high-profile cases of data leaks have been highlighted over the years in the media.
You can check if your email has previously been included in a data breach via the website found here.
Best practices for passwords:
 SSL certificates are installed on a server for this type of encryption and they are commonly renewed annually. Most server software now allows for a free SSL service. There are however other premium options available.
SSL certificates are installed on a server for this type of encryption and they are commonly renewed annually. Most server software now allows for a free SSL service. There are however other premium options available.
 Each time you return to the website and try to log in, the user table will be cross-checked against what you have inputted to find a match. Thousands of users can be stored in a single table so they are a key target for hackers looking to exploit the data and sell on via a black-market.
Passwords
The safest presumption we can make is that your password will be passed to a hacker at some point or someone with malicious intent. Commonly, a third-party website you use will be exploited and reveal your email and password in a leak. Many high-profile cases of data leaks have been highlighted over the years in the media.
You can check if your email has previously been included in a data breach via the website found here.
Best practices for passwords:
Each time you return to the website and try to log in, the user table will be cross-checked against what you have inputted to find a match. Thousands of users can be stored in a single table so they are a key target for hackers looking to exploit the data and sell on via a black-market.
Passwords
The safest presumption we can make is that your password will be passed to a hacker at some point or someone with malicious intent. Commonly, a third-party website you use will be exploited and reveal your email and password in a leak. Many high-profile cases of data leaks have been highlighted over the years in the media.
You can check if your email has previously been included in a data breach via the website found here.
Best practices for passwords:
- Change your password frequently. This will invalidate older passwords that might fall into the wrong hands and render the old data useless.
- Make them unique to each site. If your username and password details are leaked, someone with malicious intent will likely attempt to use them on other popular websites. If the password is unique, in every case, you will minimise exposure. A reasonable format for a password might be: MYPASSWORD_WEBSITENAME
 SSL certificates are installed on a server for this type of encryption and they are commonly renewed annually. Most server software now allows for a free SSL service. There are however other premium options available.
SSL certificates are installed on a server for this type of encryption and they are commonly renewed annually. Most server software now allows for a free SSL service. There are however other premium options available.
Security Basics for the Web Designer
Here are some additional basic security steps for the web designer.Scope
There are potentially many routes where a hacker might try to find an exploit. Typical sites include:- Server Ports (FTP, SSH)
- Application Admin Panel (/admin or /wp-admin)
- Application Front-end (search bars or forms)
- Server Admin Panel (Plesk, CPanel)